Blockchain Privacy Explained: Anonymity, Confidentiality, Zero-Knowledge Proofs, and Compliance
Blockchains were designed to be transparent. That transparency is powerful. It is also the source of most privacy problems.
Every transaction is recorded. Every address can be tracked. Data, once written, is hard to erase. That is great for auditability and trust. It is not great for personal data, sensitive business information, or regulated industries.
This article explains blockchain privacy clearly, without hand-waving. We will cover what privacy actually means, why it is difficult on blockchains, the main techniques used today, and how teams balance privacy with compliance and audit requirements.
If you are building, investing, or deciding whether blockchain makes sense for your use case, this guide is meant to help you make that call.
What Blockchain Privacy really means
When people say blockchain privacy, they often mean different things. That confusion causes bad design choices.
There are two core distinctions you need to understand.
Pseudonymity vs anonymity
Most public blockchains are pseudonymous, not anonymous.
A wallet address does not include your name or email. But once an address is linked to you, directly or indirectly, every past and future transaction tied to it becomes visible.
That is pseudonymity. You are hidden behind an identifier, not invisible.
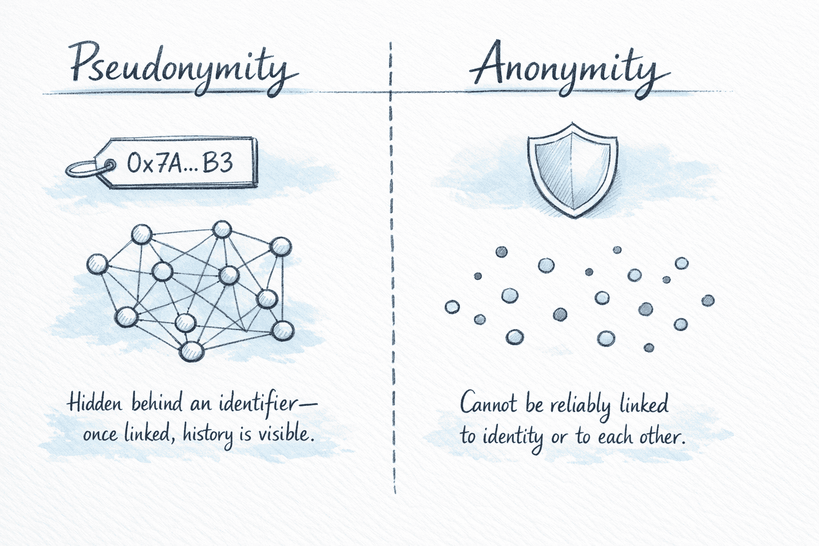
Anonymity means transactions cannot be reliably linked to a real-world identity or to each other. Achieving real anonymity on a transparent ledger is hard and usually requires specialized cryptography or protocol design.
Transaction privacy vs network privacy
Privacy also operates at different layers.
- Transaction privacy: hides details like sender, receiver, amount, or asset type.
- Network privacy: hides metadata such as IP addresses, timing, and message propagation.
You can protect one without fully protecting the other. Many systems focus on transaction privacy and leak network data, which can still be enough to deanonymize users.
Good privacy design considers both.
Why privacy is hard on blockchains (the transparency problem)
Blockchains are valuable because they are verifiable.
Anyone can independently check the ledger. Anyone can replay transactions. This removes the need for a trusted intermediary.
Privacy pushes in the opposite direction.
If you hide too much, participants can no longer verify correctness. If you reveal too much, users lose confidentiality.
This creates a structural tension:
- Transparency enables trust and auditability.
- Privacy protects users, businesses, and regulated data.
There is no free lunch. Every privacy mechanism introduces trade-offs in performance, complexity, or governance.
Understanding those trade-offs is more important than chasing perfect secrecy.
The Privacy Spectrum (a practical decision framework)
Instead of asking “Is this blockchain private?”, ask where it sits on the privacy spectrum.
Think of privacy as a set of design choices, not a binary switch.
1. Public transparency
- All data on-chain
- Anyone can read and verify everything
- Example: Bitcoin, Ethereum mainnet (default)
Pros: maximal auditability, decentralization
Cons: minimal privacy
2. Permissioned access
- Network access restricted
- Data visible only to approved participants
- Example: private enterprise chains
Pros: simpler privacy, better performance
Cons: weaker decentralization, trust assumptions
3. Anonymity
- Identities hidden
- Transactions hard to link
- Example: privacy coins with mixing or ring signatures
Pros: strong user protection
Cons: regulatory friction, limited auditability
4. Confidentiality
- Data hidden but correctness still provable
- Selective disclosure possible
- Example: zero-knowledge systems
Pros: balance of privacy and verifiability
Cons: cryptographic complexity, compute cost
5. History masking
- Past data can be concealed or abstracted
- Only commitments or proofs remain
- Example: off-chain storage with on-chain hashes
Pros: GDPR-friendly patterns
Cons: added architectural complexity
Most real systems combine several of these layers.
Techniques that enable blockchain privacy
Let’s walk through the main tools used today, what they do well, and where they fall short.
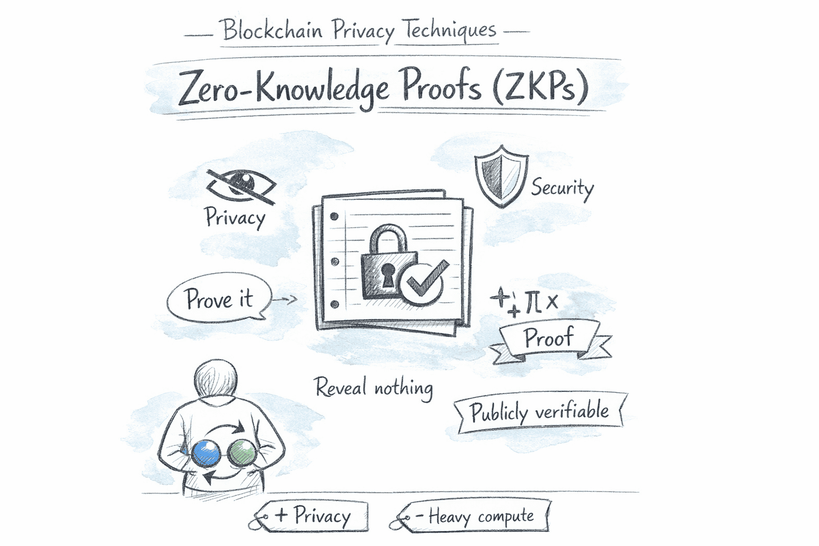
Zero-Knowledge Proofs (ZKPs / zk-SNARKs)
Zero-knowledge proofs let you prove something is true without revealing why it is true.
A simple story helps.
Imagine two balls, one red and one blue. Your friend is color-blind. You want to prove the balls are different colors without saying which is which. You hide them behind your back, swap them randomly, and ask your friend if they changed places. Repeating this proves they are different, without revealing the colors.
On blockchains, ZKPs work the same way.
You can prove:
- I have enough funds
- This transaction follows the rules
- I am over 18
- This computation was executed correctly
All without revealing balances, identities, or private inputs.
Strengths
- Strong confidentiality
- Verifiable by anyone
- Enables selective disclosure and compliance
Trade-offs
- Heavy computation
- Complex tooling
- Harder to audit and reason about
ZKPs are the backbone of modern privacy-preserving blockchains and rollups.
Ring signatures
Ring signatures let a signer blend into a group.
A transaction is signed by one member of a set, but outsiders cannot tell which one. This provides sender anonymity without needing trusted mixers.
Strengths
- No trusted third party
- Simple anonymity model
Trade-offs
- Larger transaction sizes
- Limited flexibility
- Weaker against some statistical attacks
Used heavily in early privacy coins.
Mixing and coin mixing
Mixers pool funds from many users, then redistribute them.
The idea is simple: break the link between input and output.
Strengths
- Easy to understand
- Can be added on top of existing chains
Trade-offs
- Trust assumptions
- Regulatory scrutiny
- Vulnerable to timing and amount analysis
Mixing improves privacy but rarely provides strong guarantees on its own.
Stealth addresses
Stealth addresses generate one-time destination addresses for each payment.
Only the recipient can recognize and spend the funds, even though everything is on a public chain.
Strengths
- Protects recipient privacy
- No interaction required
Trade-offs
- Sender may still be identifiable
- Requires wallet support
Often combined with other techniques.
Decentralized identity (DID)
DIDs separate identity from transactions.
Instead of reusing addresses, users prove attributes or credentials selectively.
Strengths
- Fine-grained disclosure
- Useful for enterprise and regulated use cases
Trade-offs
- Ecosystem fragmentation
- Governance and standards still evolving
Identity privacy is as much social as technical.
Hash-pinning and off-chain storage
A practical enterprise pattern.
- Sensitive data lives off-chain
- A cryptographic hash is stored on-chain
- The hash proves integrity without revealing content
If data must be updated or deleted, it happens off-chain.
Strengths
- GDPR-friendly
- Simple to implement
- Strong integrity guarantees
Trade-offs
- Requires off-chain trust model
- Not fully decentralized
This pattern is common in real production systems.
Public vs private vs hybrid blockchains: what to choose
There is no universally best choice. The right answer depends on your threat model, users, and regulatory environment.
Public blockchains
Best when:
- You need strong neutrality
- Open participation matters
- Transparency is a feature
Privacy requires advanced cryptography or careful user behavior.
Private / permissioned blockchains
Best when:
- Participants are known
- Performance and confidentiality matter
- Governance is centralized or consortium-based
Privacy is simpler but trust assumptions increase.
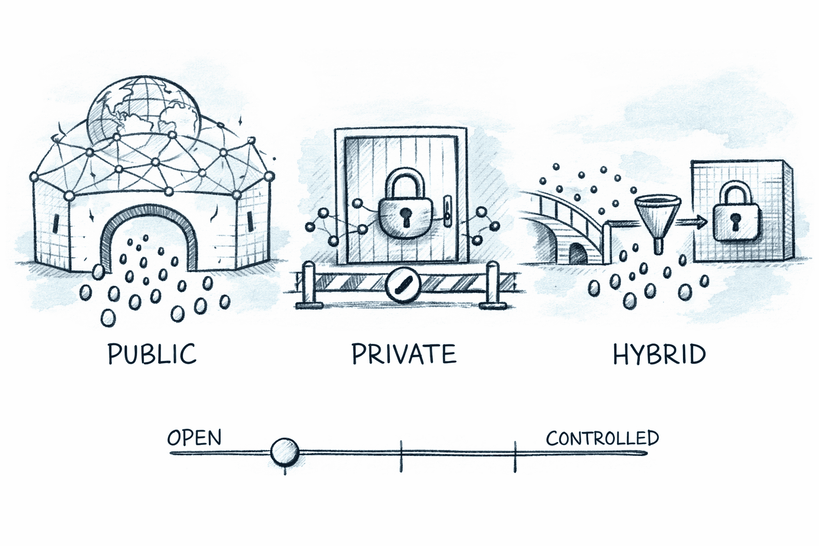
Hybrid models
Often the most realistic option.
- Public chain for settlement or verification
- Private or off-chain components for sensitive data
- Cryptographic proofs to bridge the two
This is where most enterprise blockchain designs land today.
Compliance and auditing: privacy without “going dark”
Privacy does not have to mean opacity.
Well-designed systems support selective disclosure.
Examples:
- Reveal data only to regulators
- Prove compliance without exposing raw records
- Allow audits via cryptographic proofs
GDPR and the “right to be forgotten”
Blockchains are immutable. GDPR assumes data can be erased.
Design patterns that help:
- Keep personal data off-chain
- Store only hashes or commitments on-chain
- Rotate keys instead of deleting history
- Use permissioned access where required
Privacy-by-design matters more than retrofitting fixes later.
Real-world use cases (mapped to the spectrum)
Financial services
- Confidential transactions
- Private settlement
- Proof of solvency without revealing balances
Privacy level: confidentiality + auditability
Healthcare
- Patient data off-chain
- Access controlled via cryptographic proofs
- Immutable audit trails
Privacy level: permissioned + selective disclosure
Legal services
- Document integrity
- Confidential filings
- Verifiable timestamps
Privacy level: history masking + integrity proofs
Supply chain and logistics
- Public tracking
- Hidden pricing, quantities, or counterparties
- Selective visibility for partners
Privacy level: hybrid transparency
Enterprise tokenization and EVM privacy
- Business logic on EVM
- Sensitive inputs hidden
- Proofs verify correctness
Privacy level: programmable confidentiality
Common privacy failures and pitfalls
Most privacy failures are not cryptographic. They are operational.
Address reuse
Reusing addresses links transactions. This is one of the fastest ways to lose privacy.
Identity overlap
Using the same wallet for:
- Personal use
- Work
- Governance
- Testing
This collapses separation quickly.
Metadata leakage
IP addresses, timing, and gas patterns reveal more than people expect.
False sense of anonymity
Being pseudonymous feels private until chain analysis proves otherwise.
Practical privacy hygiene checklist
- Use separate wallets for separate identities
- Avoid address reuse
- Be mindful of transaction timing
- Understand what your wallet and RPC provider log
- Do not assume default settings are private
Privacy is a process, not a feature toggle.
Further reading and learning resources
If you want to go deeper:
These are especially useful if you are building rather than just evaluating.
Final thoughts
Blockchain privacy is not about hiding everything.
It is about revealing only what is necessary, to the right parties, at the right time.
The best systems are honest about trade-offs. They combine cryptography, architecture, and governance instead of pretending one tool solves everything.
If you approach privacy as a spectrum rather than a checkbox, your designs will be stronger, more compliant, and more realistic.
Questions & Answers
Most are not. They are pseudonymous by default.
