
How Does a Hash Help Secure Blockchain Technology 2026
Modern blockchain systems are built to solve three major issues: data tampering, trust, and transparent verification. Users want assurance that once data is recorded, it cannot be altered without detection. This is exactly why the question “How Does a Hash Help Secure Blockchain Technology?” sits at the center of blockchain discussions today.
A hash function generates a fixed-length, unique digital fingerprint for every block. If even a single bit of data changes, the hash output shifts dramatically. Since each block stores both its own hash and the hash of the previous block, any manipulation immediately breaks the chain’s structure. This mechanism forms the backbone of modern blockchain security and strengthens data integrity standards in 2025.
Combined with consensus algorithms, hashing ensures that all network nodes validate and agree on the same, tamper-free ledger. In simple terms, hashing transforms blockchain into a system where trust isn’t assumed it’s mathematically enforced, making it a core pillar of modern blockchain development.
Combined with consensus algorithms, hashing ensures that all network nodes validate and agree on the same, tamper-free ledger. In simple terms, hashing transforms blockchain into a system where trust isn’t assumed and it's mathematically enforced.
How Hashing Fits Into Blockchain ?
Hashing is the backbone of blockchain design. Every block contains a block header that stores critical metadata, including the timestamp, Merkle root, and most importantly the hash of the previous block. This is the linking point that forms the chain.
When the header is processed through a cryptographic hash function, it generates a fixed-length output that represents the entire block. If anything inside the block changes, the hash changes immediately. Because each block stores the previous block’s hash, a single alteration breaks the entire chain sequence. This is why blockchain operates as an immutable ledger.
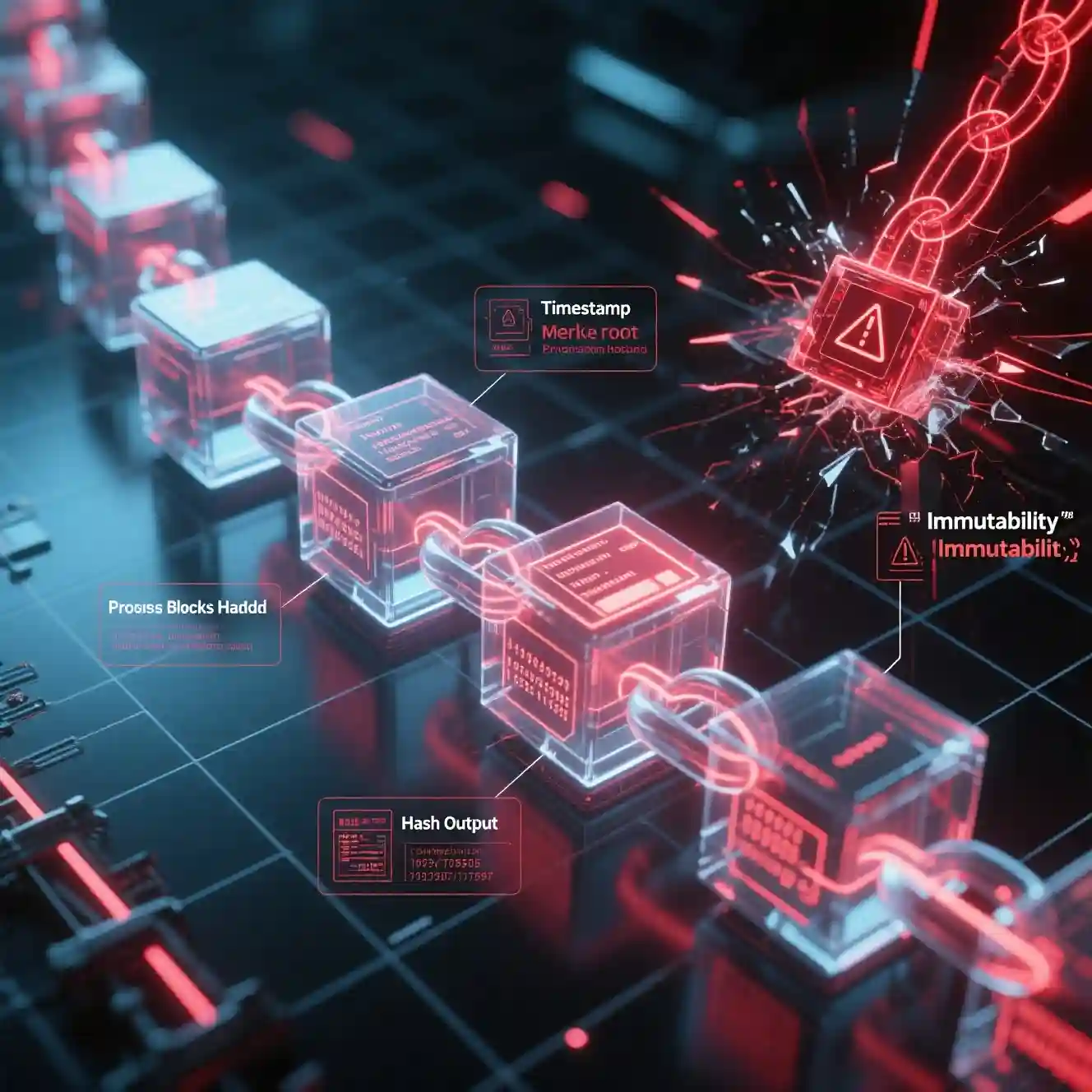
In modern networks, this creates a powerful block structure where historical data cannot be quietly edited. To change one block, an attacker would need to recompute every subsequent hash and override the network’s consensus, practically impossible in 2025.
Hashing also drives the blockchain verification process. Nodes validate incoming blocks by checking:
- Does the hash match the block’s contents?
- Does the previous-block hash correctly connect to the chain?
- Does the block satisfy consensus rules?
If any part fails, the block is rejected instantly.
This is the technical heart of immutability: hashing locks every block into its exact position, making the blockchain transparent, tamper-proof, and mathematically reliable.
How Hashing Secures Each Block in a Blockchain (Step-by-Step)
1. Data is Collected Inside a Block

Every blockchain block starts with gathering the raw information that needs to be stored permanently on the ledger. This includes key components such as:
- Transaction list: all transfers or actions waiting to be recorded
- Timestamp: the exact time the block was created
- Block number (index): the block’s position in the chain
- Additional metadata: network rules, version details, and other required fields
All of this combined forms the block data and the block header, which later play a crucial role in the block validation process. Before anything is added to the blockchain, this data is structured properly so it can be hashed, verified, and linked securely to previous blocks.
2. Hashing the Block Header (Creating the Block’s Fingerprint)

The block header (which usually includes the previous block’s hash, Merkle root, timestamp, nonce, etc.) is passed through a cryptographic hash function like SHA-256.
- Output: a fixed-length hash (e.g., 256 bits)
- This hash is the block’s unique digital fingerprint.
- This is the core of hash-based security: the hash represents the entire block’s contents in a compact way.
If any part of the header changes, the hash changes completely
3.Linking to the Previous Block (Chain Formation)
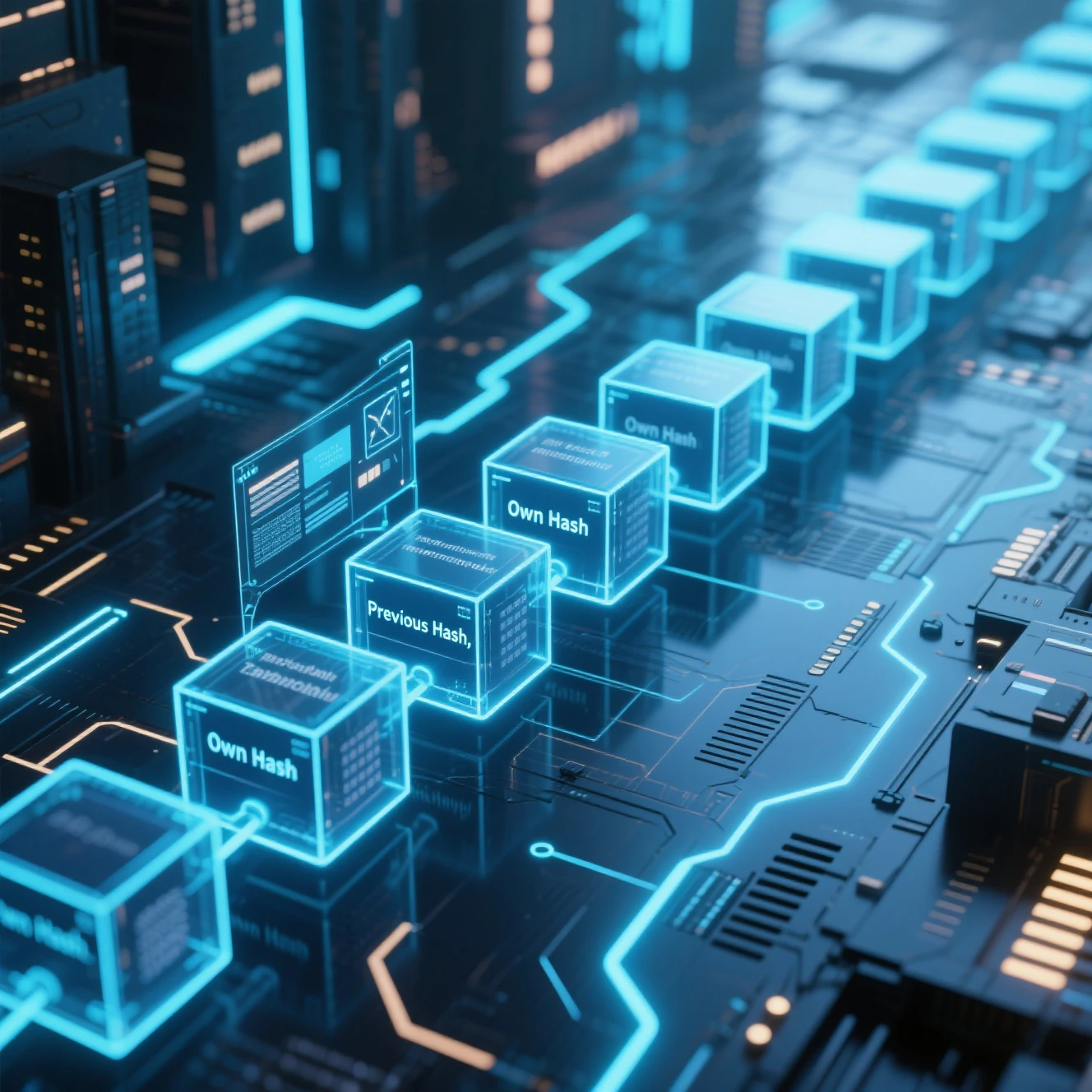
Inside the current block’s header, there is a field called previous block hash.
- This field stores the hash of the block that comes right before it.
- As a result, each block is cryptographically linked to the one before it.
This linkage creates the block structure that turns individual blocks into a chain. If someone tampers with an old block, its hash changes and then every later block’s previous hash no longer matches.
4. Proof-of-Work (Making Hashing Expensive to Cheat)

In a Proof-of-Work system, miners must find a hash that meets certain difficulty rules (for example, a hash that starts with a specific number of leading zeros).
Process:
- Miner takes the block header.
- Changes the nonce (a random number).
- Re-hashes the header.
- Repeats until the hash satisfies the difficulty target.
This makes the block validation process computationally expensive.
- Creating a valid block requires real work.
- Rewriting history means redoing that work for the target block and all blocks after it.
- This is a major part of hash-based security.
Now imagine someone tries to edit a confirmed block, maybe changing a transaction amount.
What happens?
- The block’s data changes.
- The block header’s hash is recalculated.
- The hash no longer matches the one recorded in the next block’s “previous hash” field.
- Every following block becomes invalid because their previous-hash links are now wrong.
- The network nodes quickly detect this mismatch and reject the altered chain.
- This is how hashing turns the blockchain into a tamper-evident, immutable ledger.
6. Tamper Detection (Instant Red Flags)

Now imagine someone tries to edit a confirmed block maybe changing a transaction amount.
What happens?
- The block’s data changes.
- The block header’s hash is recalculated.
- The hash no longer matches the one recorded in the next block’s “previous hash” field.
- Every following block becomes invalid because their previous-hash links are now wrong.
- The network nodes quickly detect this mismatch and reject the altered chain.
This is how hashing turns the blockchain into a tamper-evident, immutable ledger.
7. Hashing as the Security Backbone
Putting it all together:
- Data → Hashed into a unique block fingerprint
- Each block stores the previous block’s hash → forming a linked chain
- Proof-of-Work makes changing hashes expensive
- The blockchain consensus mechanism ensures only valid, correctly hashed blocks are accepted
- Any tampering breaks hashes and is instantly visible
That’s how hash-based security turns the blockchain into a structure where each block is locked in place and the entire system becomes mathematically trustworthy.
How Does a Hash Help Secure Blockchain Technology? Key Security Advantages Explained
Hashing is the core engine behind hash-based security in modern blockchains. It converts every piece of data into a unique digital fingerprint, making the network resistant to manipulation and strengthening data verification in decentralized networks. Here’s how hashing delivers real, measurable security benefits across different use cases.
1. Tamper Resistance
A hash changes completely if even one character in the data is altered.
This makes unauthorized changes instantly visible and stops attackers from silently editing blockchain records.
Real example:
If a transaction in Bitcoin is modified, the block’s hash changes and no longer matches the next block’s “previous hash.” The chain breaks, exposing the tampering immediately.
This is a powerful form of blockchain attack prevention.
2. Fraud Detection
Hash mismatches reveal any attempt to insert fake records or manipulate existing ones.
Real example:
In supply-chain networks like food tracking systems, each shipment update is hashed.
If a distributor alters an item’s origin or batch information, the hash mismatch alerts everyone in the network. Fraud becomes impossible to hide.
3. Immutability
Every block stores the hash of the previous block.This chain-like structure prevents anyone from rewriting history without recalculating thousands of hashes, something computationally unrealistic.
Real example:
In smart contract platforms, once a contract execution is recorded, it cannot be modified without breaking the hash chain, preserving long-term trust.
4. Replay Protection
Hashing helps prevent attackers from reusing old, valid transactions in new contexts.
Real example:
Cryptocurrency transfers include hashed metadata like nonces and timestamps.
Even if someone captures the original transaction, replaying it will fail because the blockchain expects a fresh state.
5. Historical Integrity
Hashing preserves the accuracy of the blockchain’s entire timeline.
Real example:
In healthcare systems using blockchain, patient records are hashed sequentially.
If anyone tries to alter a past entry, the hash discrepancy is detected instantly, maintaining reliable long-term data integrity.
Common Blockchain User Concerns and How Hashing Solves Them
Most people who use blockchain or even just hear about it worry about the same things:
Can someone change my data? What if a fake transaction gets in? How do we trust the system? Is verification too slow?
These are real blockchain problems, and hashing quietly fixes most of them behind the scenes.
Here’s the natural, practical breakdown.
1. Data Tampering
The worry:
What if someone edits a block without anyone noticing?
How hashing fixes it:
- Every block gets its own unique hash.
- Change even one tiny detail inside the block, and the hash flips into something completely different.
- And because each block also stores the hash of the block before it, any change instantly breaks the chain.
Why it matters:
Tampering becomes impossible to hide one of the strongest hashing solutions in blockchain.
2. Fake Transactions
The worry:
What stops someone from slipping a fake transaction into the system?
How hashing fixes it:
- All transactions inside a block are hashed and rolled up into something called a Merkle root.
- Nodes compare that root with what’s inside the block header.
- If someone tries to inject a fake entry, the Merkle root won’t match and the block gets rejected automatically.
Why it matters:
Only real, verified data gets in, ensuring transaction authenticity.
3. Trust Issues in a Decentralized Network
The worry:
How can I trust a system where nobody is in charge?
How hashing fixes it:
Every node checks the same things:
- The block’s hash
- The previous block’s hash
- The Merkle root
Proof-of-Work or other consensus rules
If anything feels off, the block is thrown out immediately.
Why it matters:
You don’t trust people, you trust math.
That’s real data verification in decentralized networks.
4. Slow Verification
The worry:
Isn’t checking every transaction slow?
How hashing fixes it:
- Nodes don’t verify everything line-by-link
- They check the hash and the Merkle root.
If the hash fits the data, the whole block is considered valid.
Why it matters:
Verification stays fast, even when thousands of transactions are flowing.
The Importance of Hashing in 2026-Ready Blockchain Systems
As blockchain networks grow more complex, the role of hashing becomes even more important. The future of blockchain security depends on stronger, smarter, and more adaptable hash algorithms that can handle new threats and larger global networks. Hashing isn’t just a security tool anymore, it's the foundation of next-generation cryptography and every advanced blockchain architecture being built for 2026 and beyond.
1.Quantum-Resistant Hashing
With quantum computing getting closer to real-world applications, traditional hash algorithms may eventually face new risks.
2026-ready blockchains are expected to adopt quantum-resistant hashing, which uses more advanced mathematical structures to stay secure even against quantum attacks.
This shift is part of the broader hash algorithm evolution, ensuring that blockchains remain safe long-term.
2.Network Scaling and Performance
As networks grow, blockchains must verify more transactions without slowing down.
Modern hashing techniques make this possible by enabling:
- Faster block verification
- More efficient Merkle tree updates
- Lighter validation requirements for nodes
This helps blockchains scale globally without sacrificing data integrity or security.
3.Improved Security Models
Hashing protects users against tampering, replay attacks, and data corruption.
But in next-generation systems, hashing becomes part of a deeper security model that includes:
- Multi-layer hashing (block + transaction + state hashing)
- Adaptive difficulty rules
- Enhanced protection against 51% attacks
These improvements push the boundaries of the future of blockchain security and create networks that are more resistant to both technical and economic attacks.
4.Stronger Consensus Mechanisms
Consensus systems like Proof-of-Stake, Proof-of-Work, and hybrid models all rely on hashing to validate blocks and maintain trust across decentralized nodes.
In 2026-ready systems, updated hash functions support:
- Faster finality
- More accurate block scoring
- Better fraud-proofs in Layer-2 systems
- More reliable cross-chain verification
This strengthens the entire blockchain verification process as the ecosystem expands.
The Role of Hashing in Securing Blockchain Technology
Hashing is the quiet force that keeps blockchain secure. It locks every block into place, making the ledger immutable so no one can rewrite history without being caught. It also builds trust in a system where no central authority exists; the math itself guarantees honesty. By giving each block a unique digital fingerprint, hashing makes verification fast, simple, and reliable, even as networks grow.
Most importantly, hashing gives blockchain its long-term security. From detecting tampering to powering consensus to protecting transaction history, hashing ensures the entire system stays transparent, trustworthy, and mathematically protected.
Hashing doesn’t just secure blockchain today it defines the trust, transparency, and resilience that the next decade of decentralized systems will be built on.
In the end, this is why hashing matters in blockchain. It’s the foundation of secure blockchain architecture and the reason decentralized networks can function as true trustless systems without ever relying on a single person or institution.
.
Questions & Answers
A block is locked when its data is hashed and added to the chain. Once connected to the previous block’s hash, any attempt to change it breaks the chain, making the block essentially unalterable.
Tags
About the Author
Israr Ahmed
Stay Updated
Subscribe to our newsletter for the latest articles.
Let’s Discuss Your Project
Ready to bring your idea to life? Talk with our experts today and explore the best solutions for your business.
